In This Issue
Task Force Update: Expedition XVIII – Distributed Intelligence, Massive Impact
OSINT Stories That Matter: Reflections from the Field with Liz Bradt
OSINT Tradecraft: Deepfake Detection 2 – Forensic Analysis
Who We Are
The Skull Games Task Force employs Open Source Intelligence to IDENTIFY sexual predators and their victims, enabling law enforcement to INTERDICT the cycle of abuse. Our mission is to liberate survivors and EMPOWER them with the opportunity for a life of hope, healing, and freedom. The Task Force provides direct support to law enforcement through small teams or as a massive expedition, bringing together the collective capability of more than 400 elite volunteers. This counter-sexual exploitation offensive leverages considerable expertise and resources to fight human trafficking and sexual exploitation. With us as the HUNTERS, we get into the heads of predators, in our own “SKULL GAME”…
January Operations
by Olinda Cardenas
- Predators Arrested: 27
- Victims Recovered and Offered Assistance: 5
- Individuals Trained in Countertrafficking: 330
The Skull Games Task Force launched Expedition XVIII as a fully remote deployment in January, uniting intelligence professionals across multiple locations with one shared mission: identifying victims and targeting exploiters, generating actionable leads for law enforcement partners. Over the course of the expedition, 70 volunteer “Hunters” worked collaboratively in structured OSINT cells, producing measurable and meaningful impact:
- 39 victims identified for recovery
- 18 persons of interest developed for investigative follow-up
Remote operations continue to demonstrate that geography is no longer a limitation in combating trafficking networks. Predators operate online without borders, and so do we. By combining disciplined methodology, advanced tooling, and collaborative cell leadership, Expedition XVIII reinforced the power of distributed intelligence teams working in lockstep.
OSINT Stories That Matter
by Tom Phelan and Liz Bradt
In this new section, we asked the Skull Games community for impactful stories from their work. We encourage our Hunters to share short reflections on the following:
- A moment where our work directly supported an investigation or operation.
- An insight or lesson learned that changed how they approach OSINT or analysis.
- A time when collaboration within the Task Force or with partners made a difference.
- An “aha” moment where assumptions were challenged, or clarity was gained.
- What motivates you to continue volunteering and contributing to the mission?
We want to take time to reflect on stories that focus on the work, the process, and the impact, highlighting professionalism, teamwork, and growth. Our first stories come from our Director of Operations, Liz Bradt.
Direct Support to Operations
“I often describe my path to Skull Games Solutions as being in the right place at the right time. Stepping into the role, the reality of the mission became clear very quickly. Within my first few months, I had the opportunity to support an operation as an intelligence analyst, working alongside law enforcement as they contacted victims and sought to identify a potential trafficker.
While I was physically present, I was far from working alone. A team of Task Force members supported me remotely, and that collaboration remains one of our organization’s greatest strengths. Together, we were able to positively identify a victim, an associate, and a person of interest. The intelligence we developed and shared directly informed operational decisions and helped change the course of these women’s lives. They accepted assistance, and their trafficker was arrested.
Having spent years supporting investigations from behind the scenes, this was one of my first opportunities to witness the Task Force’s work in real time. It reinforced something I already believed: the hours spent behind the screen matter. Applied OSINT makes a difference, and when done with purpose, it leads to real, measurable outcomes.”
Why I Continue to Volunteer
“When I first joined the Task Force several years ago, my understanding of trafficking was incomplete. Shaped largely by prior international experience, I didn’t yet grasp one of the most important realities of this crime: it exists in communities of every size across the United States. That perspective shifted during my first weekend supporting Skull Games, when I worked a lead that changed how I viewed exploitation.
The case centered on a teenage girl with a bright future, a standout athlete navigating the loss of a parent. What followed were small but telling changes: subtle shifts in social media behavior, a new relationship, and eventually a second online presence that looked like an entirely different person. At the time, the progression was surprising. In hindsight, it was a pattern.
Years later, I’ve learned that variations of this story are far more common than many realize. Trafficking is not always defined by dramatic moments or overt force. More often, it unfolds quietly through psychological control and gradual change. These are the indicators that matter most, and they are also the easiest to miss. Paying attention to those details is where our work begins and where it can truly make a difference.”
OSINT Tradecraft: Deepfake Detection (Part 2) – Forensic Analysis
by Tom Phelan
In Part 1, we learned that there are a couple of deepfake detectors that work (like SightEngine). These free tools are not consistently reliable. So what if you analyze an image with an AI detection tool but still don’t know if it is fake? In Part 2, we move into Manual Forensic Reconstruction. With some more tradecraft, we can do full due diligence to determine whether an image is fake or altered.
Step 1: Source & Identity
Before going too deep, determine if the image exists elsewhere. Often, a deepfake is just a real face “swapped” onto a stolen background or a GAN-generated face using a real person’s metadata.
- Facial Search: Use PimEyes or id. If a search for your target returns a match for a real person under a different name, the persona is a fabrication.
- Background Verification: Use Google Lens or Yandex Images. If you find the exact room or outdoor background in a stock photo database, the environment is a fake.
- Metadata Analysis: Drag the file into ExifTool. Check the “Software” and “History” tags. If you see remnants of Stable Diffusion, Midjourney, or Adobe Photoshop, you’ve found the smoking gun.
- The Water Mark: AI Image generators will often create visible watermarks. They’re easy enough to crop out, but check anyway. Like this one that Google Gemini AI puts in the bottom right.

Step 2: Laboratory Analysis with FotoForensics
FotoForensics is how we can manually professionalize our approach to detecting image manipulation. With this type of tool, we can look for artifacts or indications that aspects of an image have been manipulated.
- Error Level Analysis (ELA): ELA highlights the difference in compression levels.
- The Rule: In a real, unedited photo, the ELA “noise” should be uniform.
- The Red Flag: If a subject’s face glows bright white while their clothing is dark, or if a piece of gear (like a backpack) has a significantly higher contrast than the person wearing it, that object was digitally inserted.
- JPEG % (The “Export” Check): Check the estimated JPEG quality. If an image is exactly 90% or 75%, it likely didn’t come from a phone sensor; it was exported from an AI generator or a web-based editor.
- Hidden Pixels: Look for data outside the visible canvas. Often, AI-generated PNGs contain “layers” that were flattened but left metadata remnants about the generation prompt or seed.
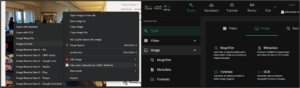
Step 3: Advanced Verification with InVID
The InVID WeVerify Plugin provides high-level forensic filters used by newsrooms and NGOs. Download the extension for your browser. Right-click your target image and select Forensic Analysis. It has explanations for every forensic tool, but basically, anything suspicious in the image will be brightly highlighted or appear as a very dark spot.
- Double Quantization (DQ): It detects if parts of an image have been compressed twice. If the subject shows a grid of red/green blocks that doesn’t align with the background, they were pasted into the scene.
- Median Noise Analysis: This filter isolates the “grain” of the image. Real camera sensors produce a consistent grain across the entire frame. AI-generated faces often appear “too smooth”—looking like a black hole or a blurry smudge—because the AI didn’t calculate the sensor noise correctly.
- JPEG Ghost Analysis: This highlights silhouettes of items that were moved or deleted. If you see a “ghost” of a second person in the noise filter who isn’t there in the original, you’ve found a manipulation.
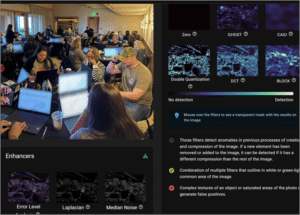
The example above is an image from a Skull Games operation. We blurred the screens for privacy. See how the blurred aspects pop out in the various detection tools?
Step 4: The Physical Reality Check
When everything falls apart, use your intuition to identify what doesn’t look right.
- Reflections: Zoom into the pupils. Real eyes reflect the environment (a window, a camera, a light). AI reflections are often asymmetrical or generic white dots.
- Anatomy: Check the intersections. Look closely at where hair passes behind an ear or where a strap meets a shoulder. AI often “blurs” these complex intersections rather than rendering them sharply.
Bottom Line: Automation finds artifacts, but humans understand situations and have gut instincts. Use these tools to move from “I suspect this is fake” to “I can prove this is a fabrication.”
Upcoming Events
- Task Force Expedition XIX | May 16 – 17 | Ybor City, FL
Skull Games Links
- Social Media: Follow Us Linkedin Facebook Insta Twitter
- Donations: Support Us
- Law Enforcement: Partner With Us
- Volunteer: Join Us
About the Author

Tom Phelan is an active-duty U.S. Army Intelligence Officer with over five years of experience in OSINT and a dedicated volunteer for Skull Games Task Force.

Olinda Cardenas is a former crime scene investigator turned cybercrime enthusiast. She specializes in OSINT and financial crime investigations and is a dedicated volunteer with Skull Games



