In This Issue
Training and Operations: Advanced Human Trafficking Training Oklahoma
OSINT Stories That Matter: Julie Beck
OSINT Tradecraft: Wartime OSINT – Iran Conflict vs. Russia Conflict
Who We Are
The Skull Games Task Force employs Open Source Intelligence to IDENTIFY sexual predators and their victims, enabling law enforcement to INTERDICT the cycle of abuse. Our mission is to liberate survivors and EMPOWER them with the opportunity for a life of hope, healing, and freedom. The Task Force provides direct support to law enforcement through small teams or as a massive expedition, bringing together the collective capability of more than 400 elite volunteers. This counter-sexual exploitation offensive leverages considerable expertise and resources to fight human trafficking and sexual exploitation. With us as the HUNTERS, we get into the heads of predators, in our own “SKULL GAME”…
February Operations
by Olinda Cardenas
- Predators and Victims Identified: 11
- Predators Arrested: 5
- Individuals Trained in Countertrafficking: 25
In February, Skull Games Solutions partnered with the Oklahoma Attorney General’s Human Trafficking Response Unit to deliver Advanced Human Trafficking Training to law enforcement agencies in the Broken Bow region.
Training equips agencies with tools to recognize indicators, investigate digital evidence, and build stronger cases. But training alone is only the first step. Action is what protects communities.
Following the training sessions, participating agencies coordinated a human trafficking enforcement operation in Idabel, Oklahoma. The operation resulted in:
- Five (5) arrests for Solicitation of Prostitution and violations of the Computer Crimes Act
Human trafficking networks rarely operate within a single jurisdiction. They cross county lines, state borders, and digital platforms. Effective response requires the same level of coordination from those working to stop them.
This operation reflected exactly that: a multi-agency effort built on shared intelligence, joint preparation, and trust between partners.
Skull Games Solutions is grateful for the continued partnership with the Office of the Oklahoma Attorney General and Attorney General Gentner Drummond, and for the commitment shown by the agencies protecting Oklahoma communities.
Participating agencies included:
- Pittsburgh County Sheriff’s Office
- Idabel Police Department
- Hochatown Police Department
- Clayton Police Department
- McCurtain County Sheriff’s Office
- Choctaw Nation Lighthorse Police
- Valliant Police Department
- Antlers Police Department
- Oklahoma Department of Corrections
- Rattan Police Department
- Pushmataha County Sheriff’s Office
Stronger partnerships. Smarter operations. Safer communities.
OSINT Stories That Matter
by Tom Phelan and Julie Beck
In this new section, we ask the Skull Games community for impactful stories from their work. We encourage our Hunters to share short reflections on the following:
- A moment where our work directly supported an investigation or operation.
- An insight or lesson learned that changed how they approach OSINT or analysis.
- A time when collaboration within the Task Force or with partners made a difference.
- An “aha” moment where assumptions were challenged, or clarity was gained.
- What motivates you to continue volunteering and contributing to the mission?
We want to take time to reflect on stories that focus on the work, the process, and the impact, highlighting professionalism, teamwork, and growth. The month’s story comes from Julie Beck.
The Weight You Don’t See: An Analyst’s View from the Inside of Human Trafficking Investigations
There are challenges in human trafficking investigations that never make it into case summaries, threat assessments, or intelligence briefings. They don’t fit neatly into a methodology section or a slide deck. But they sit with you—long after the tabs are closed, and the tools are powered down.
From the outside, investigative work can look technical: link analysis, OSINT collection, pattern recognition, timelines. From the inside, it’s human. Painfully human.
The Emotional Toll No One Trains You For
One of the hardest parts of working trafficking cases is the age of the individuals involved. Seeing very young people—sometimes children—presented through fragments of online life is deeply destabilizing. Profiles, images, captions, emojis, comments. Things that should represent innocence or self-expression instead signal coercion, fear, and survival.
As analysts, we are trained to observe, not react. To document, not intervene. To stay objective. But objectivity doesn’t erase empathy. It doesn’t stop your brain from filling in the gaps between the data points.
You see patterns others might miss: repeated phrases across posts, unnatural scheduling, signs of control masked as “relationships.” And you also see how young they are—how limited their agency truly is. That awareness carries weight. It forces you to reconcile professional distance with a very real human response: grief, anger, helplessness.
There’s a quiet moral injury that can come with this work. You know what you’re seeing matters. You know it may contribute to accountability or rescue. But you also know you are witnessing harm in near real time, often without the authority to stop it yourself.
That tension never fully goes away.

When the Data Itself Becomes the Obstacle
Beyond the emotional strain, trafficking investigations present technical challenges that are uniquely complex—and sometimes deeply frustrating.
One case that stands out involved twins.
From an OSINT perspective, twins introduce a level of ambiguity that breaks many assumptions investigators unconsciously rely on. Same birthdays, same addresses, facial similarity, shared environments, overlapping social circles, and near-identical timelines make attribution extraordinarily difficult. Automated tools struggle. Visual confirmation becomes unreliable. Even manual review can lead you down false paths.
Profiles appeared to belong to one individual—until subtle inconsistencies emerged. A tattoo that appeared in one image but not another. Slight differences in writing style. Variations in location metadata that didn’t quite line up. Each discrepancy mattered, because misattribution in a trafficking case isn’t just an analytical error—it can misdirect resources, implicate the wrong person, or obscure a victim’s actual circumstances. The challenge wasn’t just distinguishing between two individuals. It was doing so ethically and accurately, without overconfidence. OSINT thrives on pattern recognition, but this case demanded restraint: acknowledging uncertainty, documenting confidence levels, and resisting the pressure to “force” clarity where it didn’t yet exist.
It was a reminder that human beings don’t always resolve cleanly into datasets—and that some cases resist tidy conclusions.
Why This Work Still Matters
Despite the emotional cost and investigative complexity, this work matters deeply. Each accurate identification, each carefully sourced finding, each responsibly handled uncertainty contributes to a larger ecosystem of accountability and protection.
Human trafficking investigations are not just about exposing networks or documenting crimes. They are about honoring the reality of the individuals caught inside them—especially the youngest, whose voices are often the hardest to hear and the easiest to overlook.
For analysts in this space, the challenge is twofold: to sharpen our technical rigor while also acknowledging our humanity. To build better tools and methodologies, yes—but also to build better support systems for those doing the work.
Because behind every data point is a person. And behind every analyst is another human, carrying what they’ve seen, doing their best to make it count.
OSINT Tradecraft: Wartime OSINT – Iran Conflict vs. Russia Conflict
by Tom Phelan
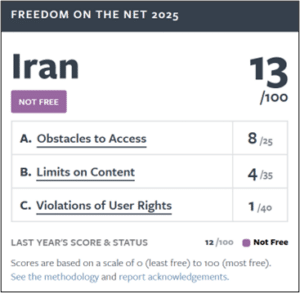
The United States is now at war with Iran. You may expect OSINT to play a huge role in this conflict like it did in the beginning of the war between Ukraine and Russia. I would challenge that assumption. Although we live in an increasingly transparent world due to modern internet technology, but Ukraine was an unusually permissive OSINT environment due to Ukrainian internet freedom. Iran conflict does not fit that same model. Iran entered a conflict already built for censorship, surveillance, and information denial. Freedom House scored Iran’s internet freedom at 13 out of 100 in 2025, while Ukraine scored 62. That gap matters immensely to analysts waiting for stories, reports or images of the conflict.

For the last two decades, Iran has prepared a sophisticated surveillance state to enable a distinct information advantage. They learned from years of Iranian civil unrest and proxy conflict, and from watching modern wars like Ukraine, the importance of information security. Tehran has built a two-sided approach: reduce what foreign intelligence services, journalists, and open-source analysts can see inside Iran, while expanding its own ability to exploit exposed digital and civilian sensors abroad.

Iranian Information Environment
Iran entered the 2025 and 2026 crises with an information environment that had already been shaped by years of censorship, filtering, and coercion. The CISES study on the 2025 to 2026 protests argues that Iran’s digital control system was already being formalized by 2001, when the regime required non-state ISPs to remove content it considered “anti-government” and to come under national authority control. There was never a realistic prospect of Ukraine-level access inside Iran because Tehran had already spent years building the technical and legal machinery needed to limit visibility from the start. When the crisis hit, the regime was not improvising; it was tightening a system it already had.
The National Information Network
The clearest expression of that system is the National Information Network, or NIN. The American Foreign Policy Council describes the NIN as the cornerstone of Iran’s authoritarian digital governance model. In practical terms, it is a domestic network architecture that allows the regime to keep critical services—banking, health care, and government—working while restricting or severing access to the global internet for the public. This makes blackouts sustainable; the regime can isolate the public without fully paralyzing the state.
Social Media
The regime has also raised the direct personal cost of documenting events. Beyond formal blocking of platforms like X and YouTube, authorities have moved toward more granular surveillance. Recent reports indicate that the regime is utilizing metadata “red-lining”, where security forces use mobile location data and device forensics to identify individuals who upload protest footage even through encrypted channels. Reuters reported in March 2026 that authorities arrested 41 people for sending videos to foreign-based media. From an analyst’s perspective, this creates a “self-censorship” loop. It dries up the flow of first-hand uploads, increases delay, weakens provenance, and leaves more room for rumor and manipulation.
Commercial Imagery
In Ukraine, commercial imagery was a “game changer.” Around Iran, the picture has been much less permissive. In March 2026, Reuters reported that Planet Labs extended delays on access to Middle East imagery from four days to fourteen days. CBS News reported that Planet and Vantor (formerly Maxar) had implemented stricter controls on imagery from parts of the Middle East. Unlike the broad commercial consensus seen in Ukraine, the current conflict has seen private-sector providers adopt more conservative risk postures, leading to significant delays for open-source researchers.
IP Cameras
Iran and other wartime actors increasingly treat internet-connected cameras as exploitable sensors. Israel and Iran go back and forth, attempting to intrude on each other’s traffic and surveillance cameras with cyber attacks. Check Point Research reportedthat during the June 2025 fighting, camera compromises were likely used to support battle damage assessment or target-correction efforts. This method apparently was critical to the targeting of Ayatollah Ali Khamenei. In response, Iran has attempted to hack cameras across the Gulf States. Iran had a massive web of cameras across the country to support their surveillance state, posing a larger weakness. This vulnerability will likely be addressed by the cybersecurity of physical destruction of cameras, including the open-source IP cameras used for OSINT.
Take Away
Open-source intelligence will not always be available the way it was in Ukraine. Crisis and conflict can change the information environment immediately, and in states like Iran, the environment may already be constricted before the first mass protest. For analysts, that means planning for denial, not just collection. Always check the freedom of internet. Archive and preserve data immediately. Plan for inconsistent civilian sensors, especially in a crisis. Witnesses can go silent, imagery can be delayed, and the best evidence can be gone before most outside observers realize the window is closing. Sometimes the hardest part of OSINT is not making sense of the data—it is recognizing that the data may never arrive.
NOTE: Any analysis or opinions suggested herein are my own and in no way represent any views or policies of the US Government.
Upcoming Events
- Task Force Expedition XIX | May 16 – 17 | Ybor City, FL
Skull Games Links
- Social Media: Follow Us Linkedin Facebook Insta Twitter
- Donations: Support Us
- Law Enforcement: Partner With Us
- Volunteer: Join Us
About the Author

Tom Phelan is an active-duty U.S. Army Intelligence Officer with over five years of experience in OSINT and a dedicated volunteer for Skull Games Task Force.

Olinda Cardenas is a former crime scene investigator turned cybercrime enthusiast. She specializes in OSINT and financial crime investigations and is a dedicated volunteer with Skull Games



